No Labels or Markers
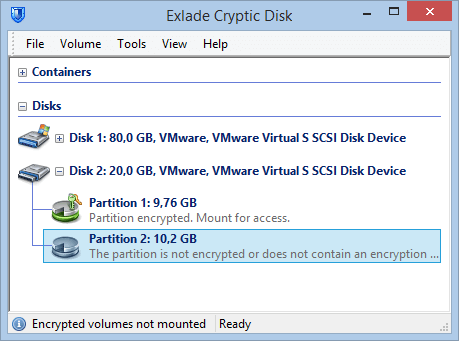
The software doesn't write any markers to the encrypted drive without the user's permission.
No marker available means no one is able to prove (without the password) that the drive contains encrypted data. The drive contents look like a random set of data.